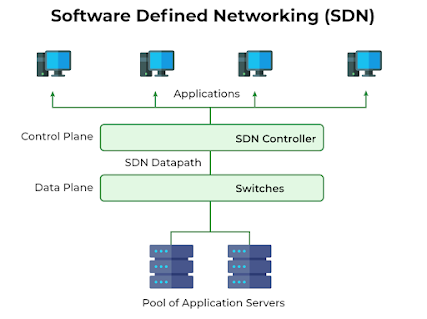
Software-Defined Networking (SDN) is an architectural approach to networking that separates the control plane from the data plane, providing centralized control and programmability to network management. In traditional networking, control functions and forwarding functions are tightly coupled in network devices like routers and switches. However, in SDN, the control plane is abstracted from the underlying hardware and implemented as software.
In an SDN architecture, there are three main components:
Data Plane: The data plane consists of network devices such as switches, routers, and access points. These devices are responsible for forwarding network traffic based on instructions received from the control plane.
Control Plane: The control plane is the brains of the SDN architecture. It consists of one or more controllers that have a global view of the network and make decisions about how network traffic should be forwarded. Controllers communicate with the data plane devices using a standardized protocol like OpenFlow.
Southbound and Northbound APIs: The southbound API is used to communicate between the control plane and the data plane. OpenFlow is one of the most common southbound APIs used in SDN. The northbound API, on the other hand, allows external applications or services to interact with the SDN controller to control and manage the network programmatically.
Comments
Post a Comment